
In recent years, the constant technological evolution has made possible a large number of advances that would have been unthinkable years ago. In industrial environments, one of the latest developments that promises to stand out and is here to stay are virtual PLC.
The virtualization of these controllers will make it possible to decouple the hardware from the software, i.e. the software will be installed in the engineering stations, while the hardware will remain in another area outside the production area.

The Industrial Internet of Things (IIoT) has experienced considerable growth in recent years, providing crucial improvements. However, it also has some limitations in terms of consumption, security, cost or scalability. In this blog, we will see how the appearance of LoRaWAN in this area can solve part of those limitations.
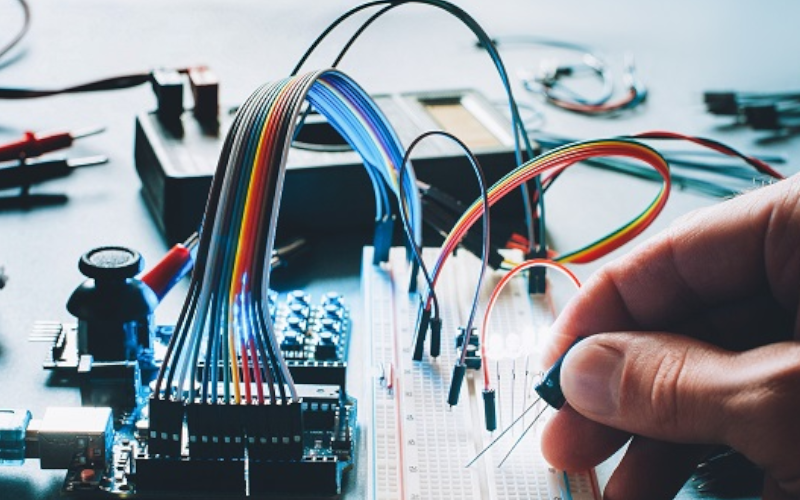
A high percentage of devices developed for the industrial world have physical interfaces that allow secondary communications to be established. These communications allow the execution of important tasks such as the management of the devices themselves or changing the way they interact with industrial processes. Although in most cases it is necessary to have physical access to the device in order to use these interfaces, manipulation of the device through these interfaces allows attackers to manipulate the operation of the system without leaving any trace if there are no mechanisms to protect the asset from hardware hacking.
This article aims to show the most widespread physical interfaces in industrial devices and embedded systems in general. On the other hand, we want to show some attacks executed throughout history in the industrial world. These attacks, thanks to the physical manipulation of a device, have allowed attackers to achieve a great impact on the targeted industrial process
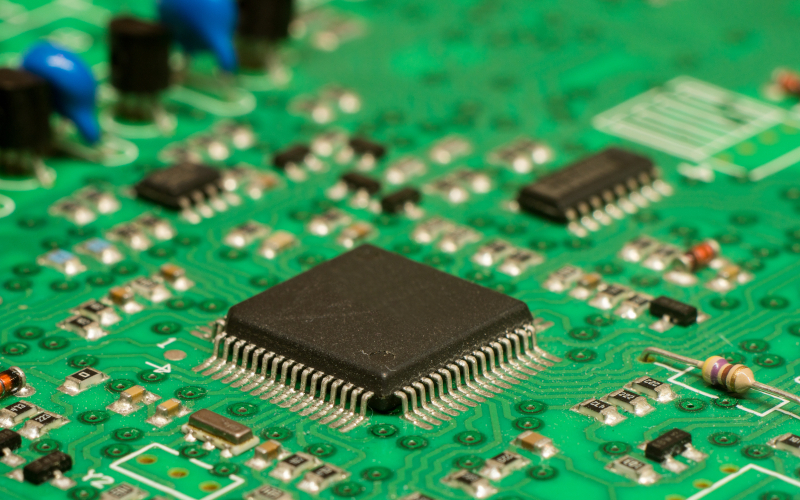
The physical protection of ports at hardware level within embedded systems allows control of the physical access interfaces, but what happens when these interfaces are necessary? Sometimes, access via JTAG or UART to systems is required for maintenance or modifications in different industrial processes. Thanks to these accesses, suppliers can access memory addresses to read or write, modify firmware, etc. Given the importance of these tasks, it is necessary to incorporate cybersecurity into the process and it is precisely on these measures that the subject of this article will focus.
Protection against fault injections, encryption of some memory sections within microcontrollers, or simple write protection are some of the defences that can be implemented to avoid problems within an industrial infrastructure

Currently, there is a constant evolution in the technologies and implementations made in Industrial Control Systems. On one hand, some of the most common implementations for the improvement of industrial systems infrastructures are digitalization and the use of cloud technology. On the other hand, the increase in communication protocols and IIoT devices (due to the growth of the Industry 4.0) generates a large volume of traffic that is difficult to control and secure.

The TETRA (Terrestrial Trunked Radio) network is a standard developed in Europe in the 1990s by ETSI (European Telecommunications Standards Institute), whose emergence came because of the management of telephone communications for extreme cases, in which standard communication via mobile might not work properly. Therefore, it can be considered as an alternative network for communications with emergency and security services to be always operational. TETRA unifies different digital radio interface alternatives for communications and serves as a standard for the construction of private mobile networks or PMR (Private Mobile Radio).

The proliferation of cybersecurity incidents in industrial environments has given rise to a huge concern in the various existing sectors. Some of them, such us the energy sector, are choosing the path taking in the banking sector with the TIBER-EU framework. In addition, many governments are allocating large sums of money to their government agencies to develop strategic plans in which that exercises are included

The programming of PLCs is a fundamental part of the initial phases when building and designing industrial plants. About that environment, the company will base all its operations in that environment making the configuration of these controllers a critical element. When it comes to programming these devices there are a series of steps and best practices that take advantage of the native functionalities available and that involve little or no need to resort to a PLC programmer, protecting the device in a simple way with minimum spend on resource.

The increase in industrial control systems and the shortcomings of those systems in cybersecurity measures have made such systems a preferred target of attacks. The number of tools designed to pose a threat to the OT sector has increased, and the use of the Incontroller tool is especially concerning.

PLCs, or Programmable Logic Controllers, have been part of industrial environments since the birth of automation. Given their evolution over time, thanks to greater intelligence, they have become a target of interest for potential attackers.



