The great robotic crusade
Posted on 27/03/2023, by
INCIBE (INCIBE)
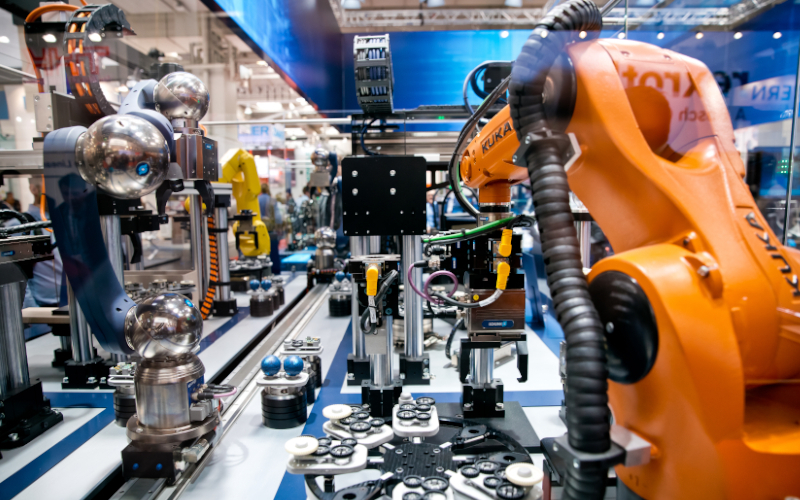
Within the industrial world, there are some sectors such as robotics, which has evolver considerably. This has led to the need to update all the regulations and standards, both in terms of physical (safety) and cybersecurity. (security). Given that the robotics sector is and will increasingly become a highly technical sector with exponential growth, the need to update all documentation has been promoted by a large group of companies in the sector, which, above all, have focused their concerns on the cybersecurity of the industrial robotics world.
Etiquetas














