
This post presents some lines of action that should be followed to deal with a DrDoS cyberattack based on the SSDP protocol, describing in detail the prevention, identification and response phases to follow.

En este post se presentan algunas líneas de actuación que deben seguirse para hacer frente a un ciberataque DrDoS basado en el protocolo CharGEN, describiendo detalladamente las fases de prevención, identificación y respuesta a adoptar.

The M-Bus protocol is a common protocol in the industry in general, it’s daily use can be related to devices for measurements of electricity, gas, water, heating, etc. This protocol has a wireless variant called Wireless M-Bus and works through a hierarchical master/slave system, standardized according to EN13757.

CAPEC (Common Attack Pattern Enumeration and Classification) is a project that focuses on enumerating and classifying common attack patterns on computer systems and providing a systematic approach to understanding and addressing the tactics used by attackers. Like CWE (Common Weakness Enumeration), CAPEC is an initiative of the computer security community and is maintained by the National Institute of Standards and Technology (NIST) in the United States. Recently in version 3.9, the project has incorporated a number of attack patterns related to the industrial world.
This article aims to show the reader the use of these codes, such as those used at the identifier level in CVEs, CWEs, etc., and which are related to many of the jobs that are carried out on a daily basis in the industrial cybersecurity sector.

The OPC UA (OPC unified architecture) communication protocol is the most modern standard presented by OPC Foundation. Currently, the OPC UA protocol is one of the most widely used in industrial environments, due to its ability to interconnect different devices, regardless of their base protocol and vendor.
Throughout this article, a technical assessment of the protocol will be conducted, explaining in detail the technical capabilities that allow a high level of cybersecurity to be implemented without causing performance losses in the devices.

Ransomware, one of the top cybersecurity threats in today's landscape, allows criminals to hijack data and demand ransoms. Although there are various families and variants, some are especially destructive. These cybercriminals have refined their methods, using everything from complex extortion to bug bounty-type programs. In the face of these challenges, we will explore tools and strategies to recover from and defend against such attacks.
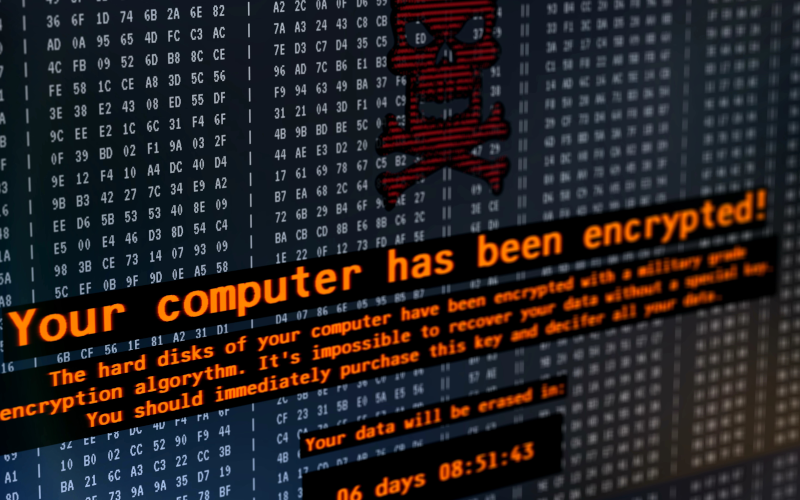
The Hive ransomware (especially in its v5 version) stands out for its sophistication, and for the impact caused to hundreds of companies and organizations worldwide, bypassing conventional defenses and challenging analysts with its advanced techniques.
In this article, we unravel its features, from its encryption methods to its anti-analysis countermeasures, illustrating not only the threat it poses, but also how it can be combated. Through a technical analysis, it is intended to empower readers with the knowledge necessary to understand and ultimately defend against these types of threats.

The Border Gateway Protocol (BGP) is fundamental to the functioning of the Internet as we know it, as it serves to route data flows along the optimal routes, through several different hops (or IPs). However, it was not designed with security by design, which opens the door to hijacking BGP-type threats.
Through these types of attacks, malicious actors can redirect traffic, causing data loss, such as in Man-in-the-Middle, among others. This article explores in depth these types of attacks, their impact, and the countermeasures available through mechanisms such as RPKI, IRR, and ROA.

The Avaddon ransomware appears as a disturbing threat that has demonstrated its ability to exploit vulnerabilities in systems, compromising the security and integrity of critical data.
This article dives into the details of how Avaddon works, while also providing a comprehensive analysis of strategies to detect and mitigate the threat.

The increase of malware specifically designed to run on systems that support industrial processes creates a need in the industry that can be partly covered by different technological solutions. This article will focus on the different options available on the market to detect malicious files that aim to modify the operation of industrial environments or simply cause denials of service.
Both portable and agent-deployed solutions can be an option, and this article will reflect on these and other options as well as provide guidelines on when it is best to use one solution or the other.



