
The M-Bus protocol is a common protocol in the industry in general, it’s daily use can be related to devices for measurements of electricity, gas, water, heating, etc. This protocol has a wireless variant called Wireless M-Bus and works through a hierarchical master/slave system, standardized according to EN13757.
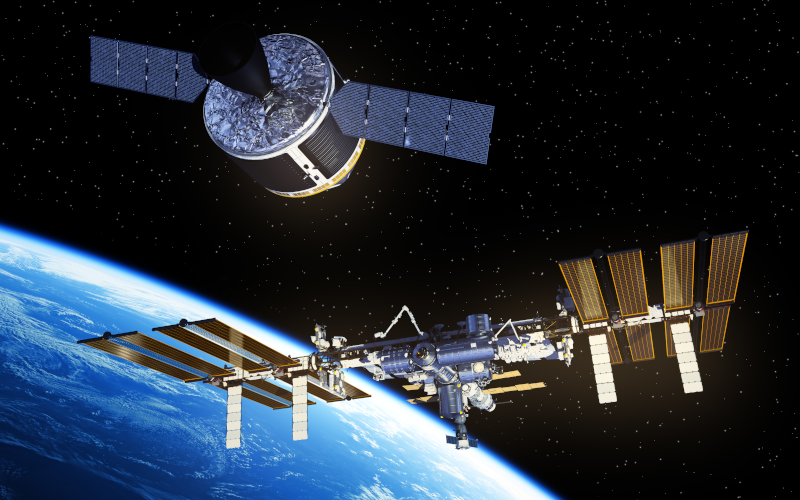
Space is an increasingly important element in the critical infrastructures of all countries. The possibility of losing or degrading space services can significantly affect both national security and all customers who have contracted services involving the use of satellites or any other space devices, resulting in major economic and security losses.
To protect it, the National Institute of Standards and Technology (NIST) has developed a cyber security framework for the commercial ground segment of the space sector, providing a means for stakeholders to assess their cyber security posture in terms of identification, protection, detection, response and recovery operations, thereby evaluating the level of risk to the satellite ground segment structure.

The OPC UA (OPC unified architecture) communication protocol is the most modern standard presented by OPC Foundation. Currently, the OPC UA protocol is one of the most widely used in industrial environments, due to its ability to interconnect different devices, regardless of their base protocol and vendor.
Throughout this article, a technical assessment of the protocol will be conducted, explaining in detail the technical capabilities that allow a high level of cybersecurity to be implemented without causing performance losses in the devices.

Second part of the Top 20 mitigations for industrial environments. This part will focus on mitigations related to network architecture, industrial protocols, network configuration and vulnerability scanning.

In the industrial world, there are a large number of systems, equipment, networks, areas, ducts, cloud environments, IT-OT environments, etc. In recent years, the number of attacks on industrial environments has been growing exponentially, and not only on purely industrial environments, but also on corporate environments that are connected to industrial environments. These IT environments being access points for attackers due to this IT/OT connectivity.

The security gaps and issues that exist within industrial environments are sometimes unknown to many information consumers. This article aims to bring first hand some of the most interesting issues and attack trends in 2023 in the industrial sector. Different industrial cybersecurity incidents so far this year will be described at a high level and a comparison will be made with the trend presented at the beginning of the year.

The Zero Trust methodology is based on the premise that no user, device, or network can be trusted, and that access privileges and security levels must be continuously verified in all interactions.
The motivation for applying the Zero Trust methodology is the need to protect a company's sensitive data and digital resources against potential internal and external threats.

Firmware analysis can help to uncover potential vulnerabilities that would otherwise never have been discovered.
Although there are multiple types of attacks on IoT and IIoT devices, this guide focuses on the firmware of these devices to check for potential vulnerabilities, using security testing and reverse engineering to allow for an in-depth analysis of the firmware.

Information security standards have become increasingly important in recent years, as more and more legal requirements oblige companies to demonstrate a certain degree of cybersecurity compliance. The IEC 62443 family of standards describes in its various sections the requirements for the secure implementation of an ICS (Industrial Control System) and represents a guarantee of cybersecurity in industrial environments. This article deals with IEC62443-3-3 covering cybersecurity of industrial systems.




