
This article aims to present a brief example guide for an implementation of the new standard in a supplier's facilities.
Going through the critical points of the standard, a generic use case will be followed to exemplify how a vehicle manufacturer can adapt its processes to comply with the new standard in an efficient and effective way.
By presenting an overview of the standard and production processes, the aim is to provide a brief guide to serve as a starting point and help avoid common failures in industrial environments when faced with new regulations, such as redundancy of effort, inefficiency in resource management and deficiencies in the application of safety measures.

MITRE Caldera OT stands out mainly for being an open-source tool that allows the simulation of different cyber-attacks in industrial environments. This tool was created by MITRE and CISA (US Cybersecurity and Infrastructures Security Agency), as the experts saw the need to be able to improve and understand cybersecurity in industrial environments without using a high number of resources.
In addition, this tool is designed to be used by both the Red Team and the Blue Team, allowing both teams to collaborate with each other to improve the level of cyber security in these environments.

Durante este artículo indagaremos en el funcionamiento y objetivos de una nueva tecnología de nueva adopción en el campo de la ciberseguridad, consistente en la creación de señuelos o información engañosa dentro de un Sistema de Control Industrial, permitiendo detectar y retrasar la intrusión de un ciberatacantes en un tiempo menor.

CAPEC (Common Attack Pattern Enumeration and Classification) is a project that focuses on enumerating and classifying common attack patterns on computer systems and providing a systematic approach to understanding and addressing the tactics used by attackers. Like CWE (Common Weakness Enumeration), CAPEC is an initiative of the computer security community and is maintained by the National Institute of Standards and Technology (NIST) in the United States. Recently in version 3.9, the project has incorporated a number of attack patterns related to the industrial world.
This article aims to show the reader the use of these codes, such as those used at the identifier level in CVEs, CWEs, etc., and which are related to many of the jobs that are carried out on a daily basis in the industrial cybersecurity sector.

IDSs are passive elements that are in our network to ensure its security, but what would happen if all our communications were encrypted, or would this protection measure be enough to ensure that my network is protected? These questions and more will be discussed in the following article to provide solutions and advice focused on industrial environments.

Demilitarized zones, also known as DMZs (demilitarized zones), are used for the secure exchange of information between computers on a network that we want to protect and an external network that needs to access those computers. DMZs are widely used in the IT sector and also in the OT sector, but the equipment and services they host are not exactly the same.
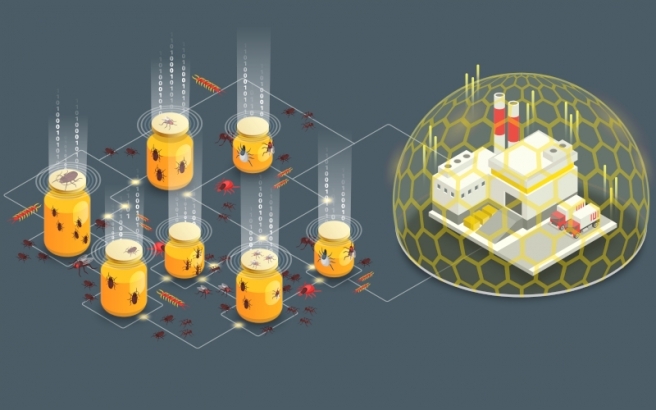
The honeypots, the recommended requirements for their correct implementation, the different possible types and their evolution until today, where they are implemented forming a honeynet.

Honeypots and their implementation in a network, known as a honeynet, are a powerful tool for defending your system and safely monitoring the attacks carried out against it. In this article we will detail what honeypots are, their implementation in OT environments, the advantages and disadvantages of their implementation in the system and the latest honeypots developed for industrial control systems.

The increasing number of attacks to industrial networks forces us to analyse their behaviour so that we can implement measures to mitigate said attacks. One of the options used to learn about the behaviour of attacks is the deployment of honeypots. This article deals with the advantages and challenges of this technology when used in industrial environments.



