
The agri-food sector is one of the most critical sectors today because it is one of the most important sectors for the country's economy, as it produces food.
This sector, like many others, is in continuous evolution. An example of this is the automation and digitalization of the many processes that are carried out. These new technologies bring many advantages, such as more efficient processes, less water consumption, detection of possible risks, etc. These great advantages also bring with them some problems, such as increased exposure to cyber-attacks.
Therefore, this article provides some basic knowledge to make the industry aware of the importance of implementing cybersecurity in their technologies.
There are currently many standards and regulations in the industrial sector. A wide variety of them allow industrial organizations to check their level of maturity, such as IEC 62443, or to improve the security level of the organization through the application of a series of guidelines, good practices or guides, as in the case of the NIST Framework.
Given the growth of the industrial sector, and the increase in capabilities, both in production and connectivity, thanks to the consolidation of Industry 4.0 and the emergence of Industry 5.0, industrial environments are in the focus, not only of technological improvements, but also of cyber-attacks.
The application and implementation of the IEC 62443 family, in combination with the NIST Framework, will enable organizations to reduce, mitigate and control the possibility of suffering a cyber-attack by implementing the controls and best practices defined in both standards.

UMAS (Unified Messaging Application Services) is a Schneider Electric (SE) proprietary protocol used to configure and monitor Schneider Electric programmable logic controllers (PLCs). While it is true that the protocol is related to this manufacturer, the use of the protocol is quite widespread in different sectors, especially the energy sector, as is obvious.
The article will focus on the technical breakdown of the protocol and the use of the protocol. The article will also show weaknesses, strengths and some technical vulnerabilities detected in this protocol.

The UN R155 and UN R156 regulations are of vital importance for vehicle cybersecurity. From July 2022, all car manufacturers that want to be type-approved must comply with both regulations, but from July 2024 this requirement will be extended to all new vehicles sold in the European Union, regardless of when the manufacturer obtained type-approval. One of the most important aspects of compliance with both regulations is the completion of a cybersecurity risk assessment of the vehicle, including all integrated components of the vehicle's supply chain. On the other hand, it also specifies how to incorporate cybersecurity from design, how to detect and respond to incidents, how to securely update vehicle software, etc.
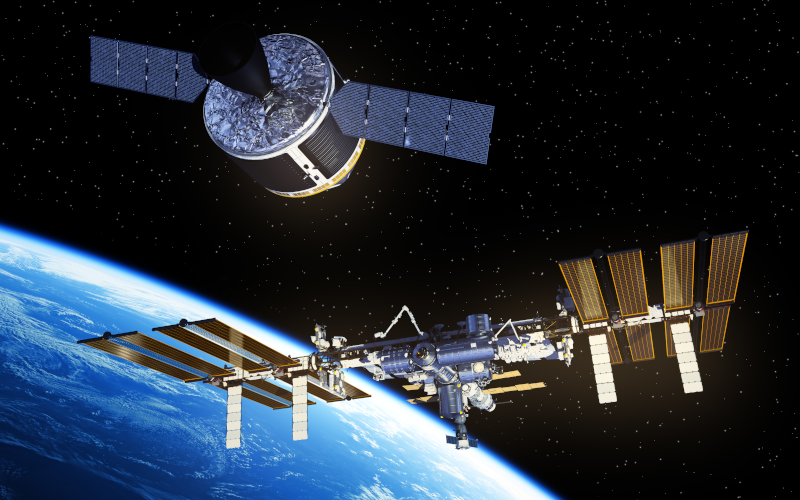
Space is an increasingly important element in the critical infrastructures of all countries. The possibility of losing or degrading space services can significantly affect both national security and all customers who have contracted services involving the use of satellites or any other space devices, resulting in major economic and security losses.
To protect it, the National Institute of Standards and Technology (NIST) has developed a cyber security framework for the commercial ground segment of the space sector, providing a means for stakeholders to assess their cyber security posture in terms of identification, protection, detection, response and recovery operations, thereby evaluating the level of risk to the satellite ground segment structure.

In the electricity sector, it has always been necessary to use robust communications that allow proper communication, since a failure in this sector would cause a large number of losses, both economic and social.
In addition, with the technological advances, it is important also to have secure communications since the electricity sector is one of the sectors that currently suffers the most cyber-attacks. For this reason, in recent years different robust and secure protocols have been created.
One of these protocols is DNP3, created mainly for the use of substation automation and control systems, for the electric utility industry, although it has now also been used for other sectors.
Finally, in this article we want to explain in more depth the operation of this protocol and the benefits or disadvantages of using this protocol.

The automotive world has always been one of the most cutting-edge sectors in terms of the technology used, which is why today's cars are equipped with technologies such as Bluetooth, NFC, GPS, etc., which improve different aspects such as comfort, fuel efficiency and increased safety.
But these implemented technologies can also bring with them serious problems, such as the risk of cyber-attacks that can affect passengers in the vehicle, both at the level of personal data and physical security.
For this reason, this article aims to provide an insight into some of the cyber-attacks that smart cars have suffered and how cyber-security is evolving and adapting to make more and more vehicles cyber-safe.

Currently, industrial infrastructures are suffering more attacks than ever before, and it is expected that attacks on these types of infrastructures will continue to grow exponentially in the coming years. This is why, throughout this article, an analysis will be made of a group of cybercriminals and their standard attack, showing how information can be obtained on the modus operandi, when and by what tactics and techniques they managed to attack an industrial infrastructure

After the pandemic, it has been observed that the healthcare sector has been one of the most attacked by cybercrimilas and organizations. This has generated a significant impact on the affected organitations, making it essencial to protect this sector due to its strategic nature and to achieve this, it is neccesary to understand its characteristics and the threats that affect it.

The OPC UA (OPC unified architecture) communication protocol is the most modern standard presented by OPC Foundation. Currently, the OPC UA protocol is one of the most widely used in industrial environments, due to its ability to interconnect different devices, regardless of their base protocol and vendor.
Throughout this article, a technical assessment of the protocol will be conducted, explaining in detail the technical capabilities that allow a high level of cybersecurity to be implemented without causing performance losses in the devices.



