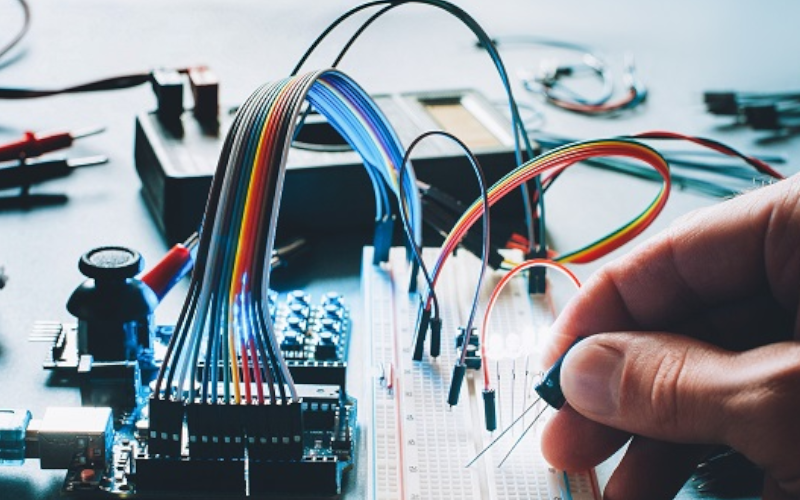
A high percentage of devices developed for the industrial world have physical interfaces that allow secondary communications to be established. These communications allow the execution of important tasks such as the management of the devices themselves or changing the way they interact with industrial processes. Although in most cases it is necessary to have physical access to the device in order to use these interfaces, manipulation of the device through these interfaces allows attackers to manipulate the operation of the system without leaving any trace if there are no mechanisms to protect the asset from hardware hacking.
This article aims to show the most widespread physical interfaces in industrial devices and embedded systems in general. On the other hand, we want to show some attacks executed throughout history in the industrial world. These attacks, thanks to the physical manipulation of a device, have allowed attackers to achieve a great impact on the targeted industrial process












