

In May 2025 the KrebsOnSecurity site suffered a massive DDoS attack of approximately 6.3 Tbps. According to the information reported, it was a brief incident ( approximately 40 to 45 seconds) designed as a test of a new IoT botnet called Aisuru. The magnitude of the attack was unprecedented: it exceeded the 2016 Mirai attack (623 Gbps) by a factor of ten. At the time, the affected entity was under the protection of Google Project Shield (free anti-DDoS service for media), and Google confirmed that this was the largest attack its infrastructure had ever suffered. This incident is a clear example that DDoS attacks are becoming more and more powerful, and can compromise even the most prepared entities, so we will explain in detail the topic of DDoS attacks.

The Initial Access tactic is one of the 12 tactics that make up the matrix developed by MITRE for industrial environments (for more information on the matrix, feel free to consult the article ICS Matrix, the State of v11). Within this tactic, different techniques used by attackers with the aim of gaining unauthorized access to an industrial environment are shown. This is often the first target of external attackers, as access to the ICS's internal environment allows internal computers to be recognized and exploited, move around the network, gain elevated privileges, or steal sensitive information. Therefore, it is important to know this tactic in order to defend our systems

This article aims to present a brief example guide for an implementation of the new standard in a supplier's facilities.
Going through the critical points of the standard, a generic use case will be followed to exemplify how a vehicle manufacturer can adapt its processes to comply with the new standard in an efficient and effective way.
By presenting an overview of the standard and production processes, the aim is to provide a brief guide to serve as a starting point and help avoid common failures in industrial environments when faced with new regulations, such as redundancy of effort, inefficiency in resource management and deficiencies in the application of safety measures.

A CI/CD (Continuous Integration/Continuous Deployment) pipeline is an essential tool in modern software development, which allows you to automate and optimize the entire development lifecycle, from code integration to its deployment in production. The article aims to explain security in CI/CD pipelines, motivating readers to adopt automated practices that not only optimize software development, but also minimize the associated risks. Keep in mind that automation carries certain risks if not handled safely, as it can increase the attack surface for cybercriminals. It underscores the importance of implementing security controls at every stage of the pipeline, urging developers to take initiative-taking steps to protect their code, their environments, and ultimately, their final products.

The increasing development of malware targeting the industrial world has not halted its momentum in the slightest. Several research groups have detected a new malware called Fuxnet and are currently investigating its scope. This malware has the capability to send specific requests at the serial level, via RS485/MBus, executing floods to more than 87.000 assets, including control systems and integrated sensors deployed across different sectors. Among the infrastructures compromised by this malware, we find hospitals, airports and other critical infrastructures that provide essential services to the population.

MITRE Caldera OT stands out mainly for being an open-source tool that allows the simulation of different cyber-attacks in industrial environments. This tool was created by MITRE and CISA (US Cybersecurity and Infrastructures Security Agency), as the experts saw the need to be able to improve and understand cybersecurity in industrial environments without using a high number of resources.
In addition, this tool is designed to be used by both the Red Team and the Blue Team, allowing both teams to collaborate with each other to improve the level of cyber security in these environments.
In the era of interconnection and digitization, industrial control systems (ICS) are increasingly exposed to cyber threats. These systems are vital for energy production, manufacturing and critical infrastructure management, and their protection has become an essential priority.
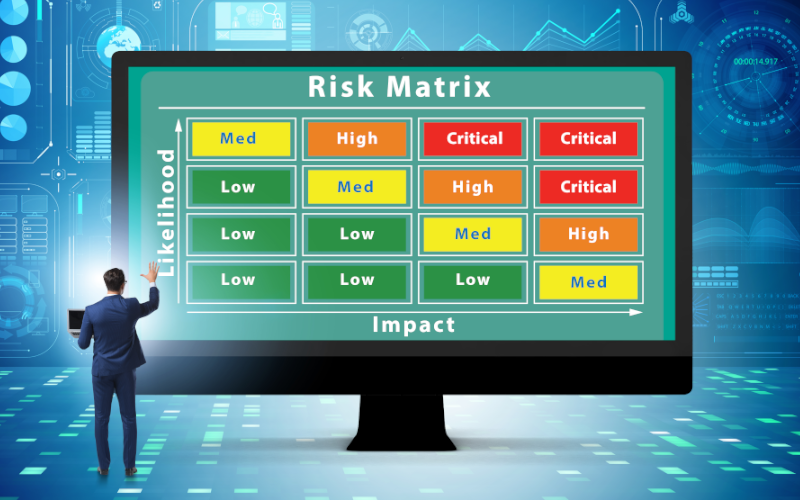
Risk analysis is fundamental in this context, as it allows identifying, assessing and prioritizing the risks that can affect ICS. This process, ranges from technical vulnerabilities to emerging threats, and is crucial for developing effective mitigation and protection strategies.
In this article, the challenges and solutions related to risk analysis in ICS will be explored, as well as the importance of the IEC 62443-3-2 standard in this critical process.
The digital twins are virtual recreations of real-world objects or processes. This innovative idea, proposed by Dr. Michael Grieves, has become increasingly relevant in various industrial sectors thanks to the advancement of technologies such as 3D modelling, the Internet of Things (IoT), the IIoT (Industrial Internet of Things), machine learning and big data. Its application makes it possible to simulate and analyse physical processes efficiently, thus contributing to the digital transformation of industry, also known as Industry 4.0.
The fundamental purpose of digital twins is to facilitate the understanding of how elements operate in the physical world. For example, in manufacturing, it is possible to create a digital twin of a factory and through simulations explore different scenarios: what would happen if a machine were modified, how would it impact production, and what would happen if a machine were changed? The digital twin provides answers before real changes are made to the physical environment, speeding up decision-making and optimising processes.

The ability to monitor and analyze the behavior of users and entities becomes crucial for early detection and response to potential threats. UEBA solutions identify unusual or anomalous patterns in user behavior, enabling rapid identification of internal threats or external compromises. This post focuses on how UEBA analysis is becoming an essential tool for a cybersecurity strategy, from identifying suspicious behavior to preventing potential security breaches.



